Documentation Index
Fetch the complete documentation index at: https://docs.gc.ai/llms.txt
Use this file to discover all available pages before exploring further.
🔐 What is SSO?
Single Sign-On (SSO) lets your team sign in to GC AI using your organization’s existing identity provider (IdP). GC AI supports SSO through WorkOS, which is compatible with any IdP that supports SAML or OIDC protocols.📋 Prerequisites
Before you begin SSO setup:- You must be an Admin in your GC AI organization
- Your organization must use an IdP that supports SAML or OIDC (e.g. Okta, Azure AD, OneLogin, Google Workspace, JumpCloud)
- You need access to your IdP’s admin console to create a new application
- Domain verification must be completed before SSO can be enabled
🌐 Step 1: Verify Your Domain
- Navigate to Organization Settings.
- Scroll down to Domain verification.
- Select Generate Link and open the link. It directs you to the domain verification process.
- Complete domain verification by following the on-screen instructions.
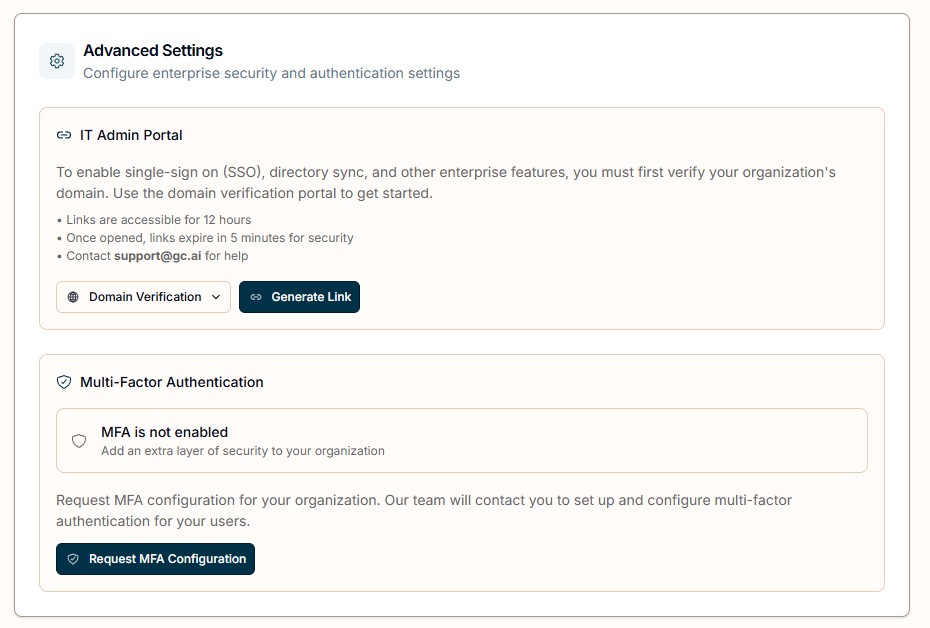
🔗 Step 2: Generate the SSO Configuration Link
- Navigate back to Organization Settings.
- Select SSO Setup from the dropdown menu.
- Select Generate Link and open the link.
🏢 Step 3: Select Your Identity Provider
Select your IdP from the list (Okta, Azure AD, OneLogin, etc.) and follow the on-screen instructions to connect it.Custom SAML or OIDC
If your IdP is not listed, select Custom OIDC or Custom SAML depending on the protocol your organization uses.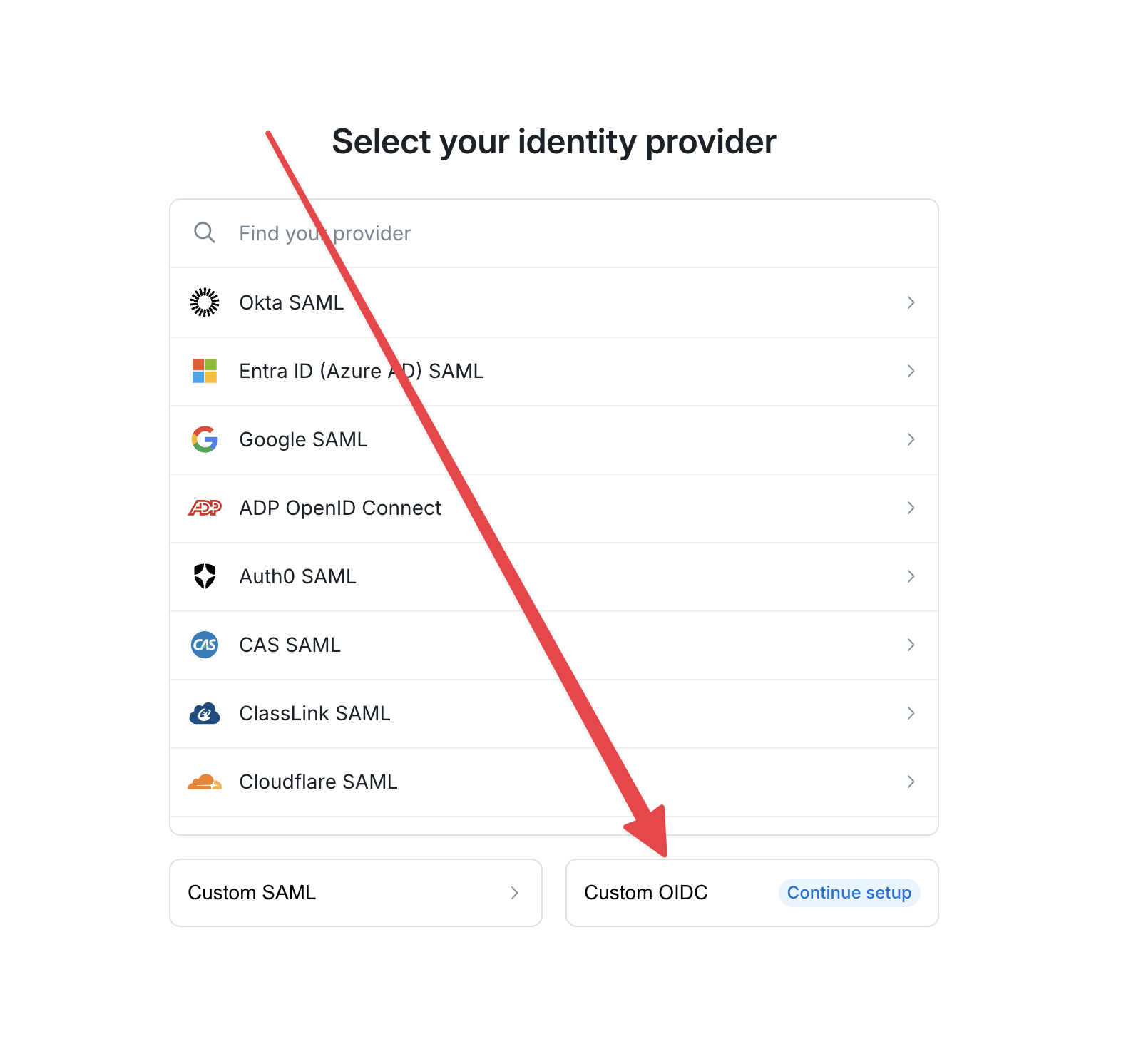 For Custom OIDC:
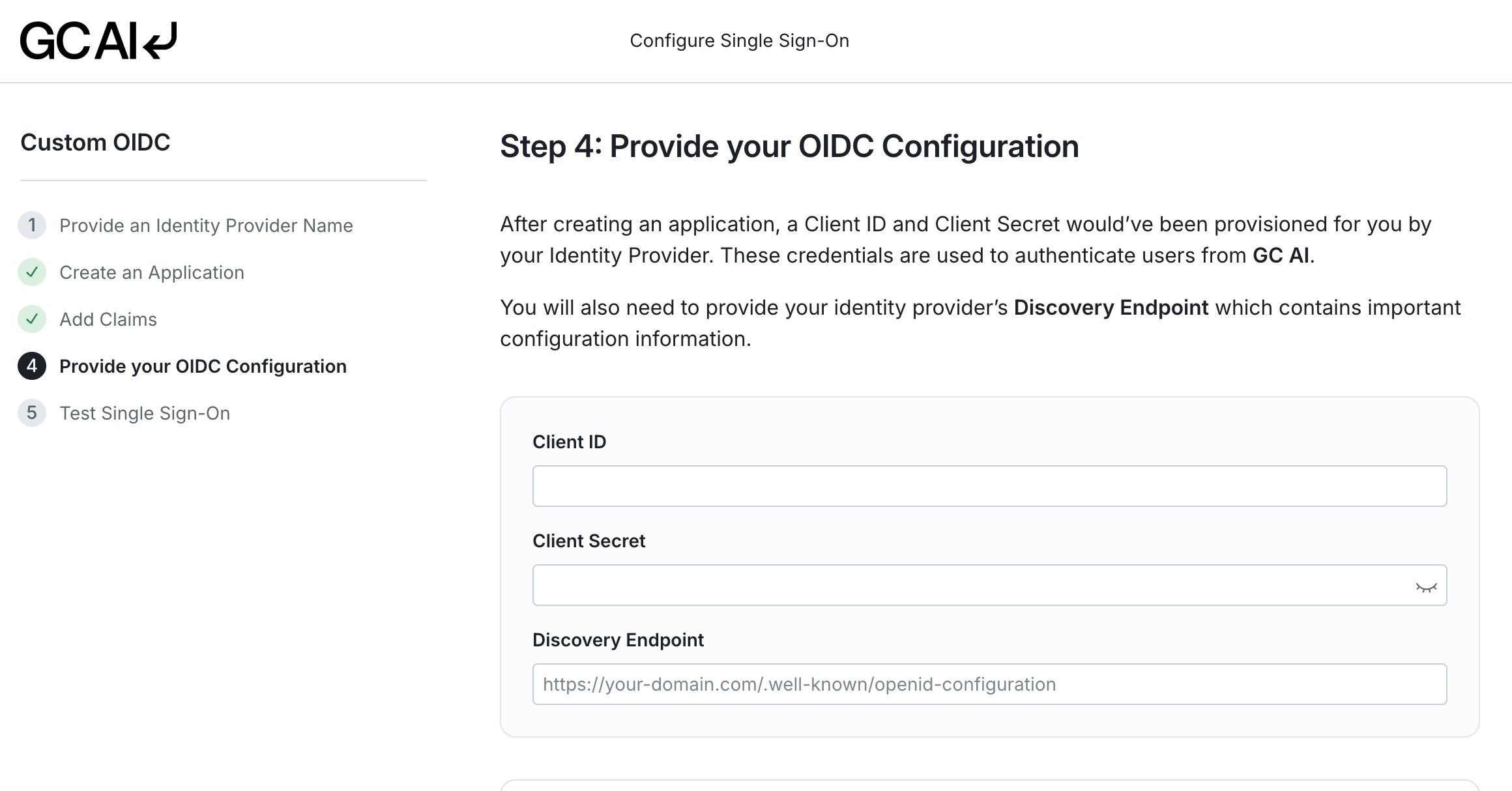
For Custom OIDC:
- Provide an IdP name.
- Copy the Redirect URI from the “Create an Application” step and add it to your IdP.
- Add the required claims to your auth token as shown on screen.
- Enter your Client ID, Client Secret, and Discovery Endpoint from your IdP.
 For Custom SAML:
For Custom SAML:
- Provide an IdP name.
- Copy the ACS URL and SP Entity ID from the setup screen into your IdP’s SAML application configuration.
- Configure the required attribute mappings in your IdP. At minimum, these attributes must be included in the SAML assertion:
id- A unique user identifieremail- The user’s email addressfirstName- The user’s first namelastName- The user’s last name
- Upload your IdP’s metadata XML or manually enter the SSO URL and X.509 certificate.
✅ Step 4: Test the Connection
After completing the configuration, select Test Connection to verify everything works. A successful test confirms that your IdP and GC AI can communicate properly. If the test fails, see the troubleshooting section below.🔧 Common Setup Issues
SAML Test Connection Fails
If you run a test of your SAML SSO connection and it does not pass, the most common causes are: Missing or incorrect attribute mappings Your IdP must send the required attributes (id, email, firstName, lastName) in the SAML assertion. If any are missing or mapped to the wrong field names, the connection test fails.
How to fix:
- Open your IdP’s admin console and navigate to the GC AI SAML application.
- Check the attribute statements (sometimes called “attribute mappings” or “parameters”).
- Verify each required attribute is mapped to the correct user field in your directory.
- Save and re-run the test.
- Go back to the SSO configuration link in GC AI and copy the ACS URL and SP Entity ID exactly as shown.
- Paste them into your IdP’s SAML application settings, replacing any previous values.
- Save and re-run the test.
- Download a fresh copy of your IdP’s metadata XML or X.509 certificate.
- Re-upload it in the GC AI SSO configuration.
- Save and re-run the test.
OIDC Test Connection Fails
Invalid Client ID or Client Secret If the credentials entered during setup don’t match what your IdP issued, authentication fails. How to fix:- Open your IdP’s admin console and locate the GC AI OIDC application.
- Copy the Client ID and Client Secret directly from your IdP.
- Re-enter them in the GC AI SSO configuration.
- Save and re-run the test.
/.well-known/openid-configuration).
How to fix:
- Verify the discovery endpoint URL in your IdP’s documentation.
- Confirm it is accessible by opening it in a browser. You should see a JSON document.
- Update the URL in the GC AI SSO configuration and re-run the test.
Domain Verification Not Completing
If domain verification stalls or fails:- Confirm you added the required DNS TXT record to your domain’s DNS settings.
- DNS changes can take up to 48 hours to propagate. Wait and try again.
- Verify the TXT record value matches exactly what GC AI provided (no extra spaces or characters).
Still Having Trouble?
If you’ve worked through the steps above and the connection test still fails, email support@gc.ai with:- Your organization name
- The IdP you are using (e.g. Okta, OneLogin, Azure AD)
- A screenshot of the test result or error message